If you’re running a mental health practice, HIPAA compliance is mandatory. It protects sensitive patient data, particularly psychotherapy notes and electronic health records. Non-compliance can lead to fines, legal issues, and loss of trust. Here’s what you need to know:
- Appoint a Compliance Officer: Assign a Privacy and Security Officer to oversee policies, risk assessments, and training.
- Perform Risk Assessments: Identify vulnerabilities, document findings, and address risks annually or after major changes.
- Implement Safeguards: Use administrative, physical, and technical measures like encryption, access controls, and secure storage.
- Train Staff: Ensure all staff complete HIPAA training before handling patient data, with annual refreshers.
- Use HIPAA-Compliant Tools: Choose software with encryption, multi-factor authentication, and signed Business Associate Agreements (BAAs).
- Manage Psychotherapy Notes: Keep them separate from general records and require explicit patient authorization for disclosure.
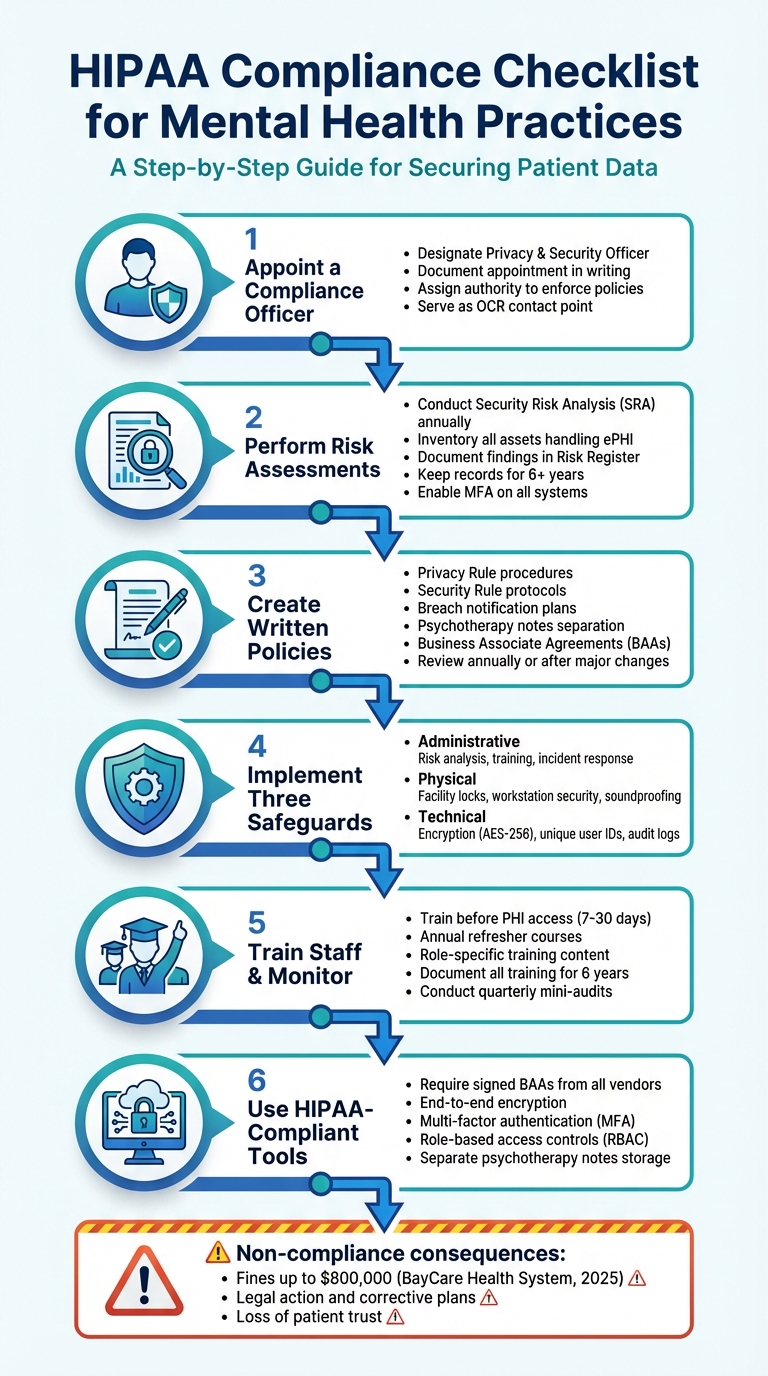
HIPAA Compliance Checklist for Mental Health Practices: 6 Essential Steps
HIPAA Compliance for Therapists: Common Scenarios and What to Do
sbb-itb-ce1c1e8
Assign a HIPAA Compliance Officer and Perform Risk Assessments
HIPAA regulations require every mental health practice to appoint both a Privacy Officer and a Security Officer. According to the law, "A covered entity must designate a privacy official who is responsible for the development and implementation of the policies and procedures of the entity". In smaller practices, a single person – such as an office manager or lead clinician – can take on both roles, as long as the appointment is documented in writing [12, 16].
Skipping this step puts your practice at risk. For example, in 2021, a pediatric clinic was fined $10,000 by the Office for Civil Rights (OCR) for failing to designate a Privacy Officer and train staff accordingly. This resulted in a corrective action plan.
The compliance officer’s role involves managing HIPAA policies, conducting annual Security Risk Analyses (SRAs), overseeing Business Associate Agreements (BAAs) with vendors (like EHR or billing services), coordinating staff training, and responding to breaches [11, 12]. They also handle sanctions for privacy violations and manage patient requests for record access or amendments [11, 5].
Responsibilities of the HIPAA Compliance Officer
The compliance officer’s duties span three key safeguard areas:
- Administrative safeguards: Conducting risk analyses, designing workforce training programs, and managing BAAs.
- Physical safeguards: Ensuring controlled facility access and maintaining secure physical spaces.
- Technical safeguards: Setting up unique user IDs, encryption protocols, and audit logs for systems managing electronic protected health information (ePHI) [1, 12].
Mental health practices face additional challenges. For instance, psychotherapy notes must be kept separate from general medical records due to their heightened protection [2, 13]. Practices treating substance use disorders must also comply with 42 CFR Part 2. By February 16, 2026, updates to the Notice of Privacy Practices will be required to reflect these enhanced protections.
The compliance officer also acts as the main point of contact for patient complaints and OCR inquiries. Their contact information must be included in the Notice of Privacy Practices. To be effective, this role needs the authority to enforce compliance and discipline staff who violate policies [11, 12].
How to Conduct a Risk Assessment
Failing to complete a Security Risk Analysis (SRA) is one of the most common reasons for OCR enforcement actions. Practices must perform an SRA at least once a year or whenever significant changes occur, such as adopting new software, relocating, or adding telehealth services [1, 12, 14].
Start by defining the scope. Include every location, system, device, and vendor that handles ePHI [1, 12]. Map out how patient information flows through your practice – from intake forms and session notes to billing and storage. For small to medium-sized practices, the U.S. Department of Health and Human Services (HHS) provides a free Security Risk Assessment Tool at HealthIT.gov [14, 15].
Next, inventory your assets and identify potential threats. Common risks include human error, unauthorized access, device theft, ransomware, and phishing attacks [1, 12]. Assess each risk based on its likelihood and potential impact on patient confidentiality. Document these findings in a Risk Register, which should outline vulnerabilities, assign mitigation responsibilities, and set deadlines for resolution [1, 5].
Keep all compliance records, including risk assessments, for at least six years [5, 12]. By 2026, practices must also maintain a technology asset inventory and a network map showing how ePHI moves through their systems. Additionally, updated regulations will require critical systems to be restored within 72 hours of a security incident.
Enable multi-factor authentication (MFA) for all systems containing ePHI. Under the 2026 requirements, MFA will be virtually mandatory as it’s one of the strongest defenses against unauthorized access [12, 17]. Ensure every vendor has a signed BAA, and review their compliance annually [1, 5, 12]. Modern standards also call for vulnerability scans every six months and annual penetration testing.
Thoroughly documented risk assessments are the cornerstone for building effective HIPAA policies and procedures.
Create and Document HIPAA Policies and Procedures
Written policies are the backbone of handling Protected Health Information (PHI) and prove diligence during OCR reviews. As HIPAA consultant Kevin Henry aptly puts it:
If it is not documented, it did not happen. – Kevin Henry, HIPAA Consultant
Mental health practices face unique challenges, managing both standard records and highly sensitive psychotherapy notes. These notes must be stored separately from general medical records and require distinct patient authorization for most disclosures. Practices treating substance use disorders must also adhere to 42 CFR Part 2, which enforces stricter confidentiality rules than HIPAA.
Your policies should encompass the Privacy Rule (e.g., minimum necessary standards, patient rights, disclosure tracking), the Security Rule (e.g., access control, encryption, audit reviews), and Breach Notification (e.g., incident response). Records management procedures are equally essential, including retention schedules. HIPAA mandates keeping compliance documentation for at least six years from its creation or last effective date.
Additionally, ensure you have signed Business Associate Agreements (BAAs) with all vendors handling PHI, such as EHR providers, billing services, telehealth platforms, and cloud storage providers. For remote work or personal device usage, enforce encryption, screen locks, and remote wipe policies. These measures should be clearly outlined in your policies.
Required Policies for Mental Health Practices
Mental health practices need tailored policies to address their unique compliance needs. Start with administrative safeguards, such as appointing Privacy and Security Officers in writing, defining role-based access controls, and enforcing sanctions for non-compliance.
The Notice of Privacy Practices (NPP) is a must-have document that explains how PHI is used, outlines patient rights, and provides instructions for filing complaints. It should be presented at the first service encounter, along with a request for written acknowledgment. Patients also have the right to access their records within 30 days of a request, with a single 30-day extension allowed if documented.
Psychotherapy notes require extra care. Keep them separate from standard medical records and ensure your EHR system excludes them from patient portals and workflows. Any disclosure of these notes should require a separate, explicit authorization.
Here’s a breakdown of key policy categories and their documentation requirements:
| Policy Category | Key Requirements | Documentation Needed |
|---|---|---|
| Privacy Rule | Minimum necessary standard, patient rights (access, amendment), NPP | NPP acknowledgments, disclosure logs |
| Security Rule | Access management, encryption, multi-factor authentication, automatic logoffs | Risk analysis, audit reports, device inventory |
| Psychotherapy Notes | Segregation from medical records, separate authorization for disclosure | Separate authorizations, storage logs |
| Breach Notification | 60-day notification for breaches affecting 500+ individuals, risk assessments | Incident reports, risk assessments, notification templates |
| Records Management | Retention schedules and secure disposal methods | Disposal certificates, chain-of-custody logs |
For breaches involving 500 or more individuals, notify the media and federal authorities within 60 days of discovery. Smaller breaches require annual reporting. Every incident should include a four-factor risk assessment to determine notification requirements.
How to Update and Review Policies
HIPAA compliance isn’t a one-and-done task – it’s an ongoing process. Policies should be reviewed and updated regularly, at least once a year, or whenever significant changes occur, such as adopting a new EHR system, adding telehealth services, relocating your practice, or changes to federal or state laws.
Standardize your policy format with sections for Statement, Purpose, Scope, Definitions, Responsibilities, Procedures, and Training. Use version control to track approval dates and review cycles, demonstrating your commitment to compliance. Store these policies in a central location for easy access.
State laws often impose stricter requirements than HIPAA. For instance, many states mandate retaining psychotherapy records for 7 to 10 years, exceeding HIPAA’s six-year minimum. Document every policy update and maintain a history of previous versions. When risk assessments reveal vulnerabilities, update related policies immediately and retrain affected staff. Consistently revising your policies is key to maintaining compliance.
Set Up Administrative, Physical, and Technical Safeguards
HIPAA mandates three layers of safeguards – administrative, physical, and technical – to protect patient information. Each layer addresses specific vulnerabilities, ensuring a comprehensive approach to security. For mental health practices, for example, safeguarding psychotherapy notes and soundproofing consultation rooms are essential to prevent accidental disclosures.
"Administrative Safeguards… serve as the operational backbone of a secure environment for Protected Health Information (PHI)." – Complydome
These safeguards work in tandem: administrative policies control access to sensitive information, physical measures secure facilities and workstations, and technical protocols protect electronic data. Ignoring these requirements can lead to costly consequences. Take BayCare Health System, which faced an $800,000 settlement in 2025 for failing to monitor system activity adequately. Together, these measures create a solid foundation for HIPAA compliance.
Administrative Safeguards
Administrative safeguards focus on management policies and processes to protect patient data. Start by appointing a HIPAA Security Officer – a designated individual responsible for overseeing compliance and serving as the main contact during audits. Conduct a formal risk analysis annually or after significant changes, and update your risk management plan as needed.
Access control is another key element. Implement role-based access, ensuring employees can only access the information necessary for their roles. Require unique user IDs for all staff – shared logins are a no-go. When an employee exits, immediately revoke their access and document the action.
Prepare for potential breaches by establishing clear incident response procedures to identify, report, and address security issues. Train all staff, including contractors and volunteers, on HIPAA requirements during onboarding and at least once a year. Keep training records for six years. Finally, develop a contingency plan that includes data backups, disaster recovery strategies, and emergency protocols to maintain operations during disruptions.
| Administrative Safeguard | Required Documentation | Frequency |
|---|---|---|
| Risk Analysis | Threat/vulnerability mapping and risk register | Annual or after changes |
| Security Officer | Written designation in job description | Upon hire/assignment |
| Workforce Training | Logs, curricula, and comprehension scores | Onboarding and annually |
| Incident Response | Logs, breach assessments, and notification copies | As incidents occur |
| Contingency Plan | Backup logs and disaster recovery test results | Annual testing |
| Business Associates | Signed BAAs for all vendors | Annual review |
Physical Safeguards
Physical safeguards protect your facility, workstations, and paper records from unauthorized access or theft. Use facility access controls like locks, key cards, or biometric systems to limit entry to areas containing sensitive information. Visitor sign-in procedures, badges, and escort protocols can further prevent unauthorized access.
Workstation security is equally important. Position computers away from public view (e.g., not facing waiting areas), and use privacy screens to reduce the risk of "shoulder surfing." Set devices to auto logoff after 5–10 minutes of inactivity, and enforce sign-out protocols. A clean desk policy can also help prevent sensitive information from being left out in the open.
For paper records, store them in locked cabinets with restricted access. Psychotherapy notes should be kept separate from general medical records to ensure their additional legal protections. Soundproof consultation rooms or use sound-masking devices to prevent conversations from being overheard.
"It only takes a single unlocked door, unattended laptop, or misplaced USB drive to compromise thousands of patient records." – Complydome
Portable devices like laptops, tablets, and USB drives are common sources of breaches. Encrypt all portable media and maintain an inventory log that tracks serial numbers, assigned users, and assignment dates. When not in use, store these devices in locked drawers. For disposal, use certified wiping services or physically destroy electronic media. For paper records, cross-cut shredders or certified destruction services are essential.
Technical Safeguards
Technical safeguards directly protect electronic data. Start with unique user IDs to manage access, and set up emergency "break-glass" protocols for urgent situations. Enforce automatic logoffs for inactive sessions and require multi-factor authentication (MFA) for accounts accessing sensitive data.
Encryption is a must. Use AES-256 encryption for data at rest, and secure data in transit with TLS 1.2 or higher. Failure to encrypt can be costly – Syracuse ASC faced a $250,000 settlement in 2025 for unencrypted devices and poor access controls.
Audit controls are another critical component. Enable logging on systems containing electronic protected health information (ePHI) and review logs at least quarterly. Automated Security Information and Event Management (SIEM) systems can flag suspicious activities, such as failed logins or after-hours access.
For psychotherapy notes, store them in a separate EHR repository with restricted access, ensuring they are excluded from general patient portals and record exports. Use integrity controls like hashing (e.g., SHA-256) to verify that ePHI remains unaltered.
| Technical Safeguard | Implementation Requirement | HIPAA Section |
|---|---|---|
| Unique User Identification | Assign unique IDs; no shared logins | § 164.312(a)(2)(i) |
| Emergency Access | Procedures for "break-glass" access | § 164.312(a)(2)(ii) |
| Automatic Logoff | Enforce timeouts for inactive sessions | § 164.312(a)(2)(iii) |
| Encryption (At Rest) | Use AES-256 for disks and databases | § 164.312(a)(2)(iv) |
| Audit Controls | Generate and routinely review activity logs | § 164.312(b) |
| Integrity | Use hashing/checksums to detect alteration | § 164.312(c)(1) |
| Authentication | Verify identity via MFA, passwords, or biometrics | § 164.312(d) |
| Encryption (In Transit) | Use TLS 1.2+ or VPNs for data movement | § 164.312(e)(2)(ii) |
Handle Psychotherapy Notes and Patient Rights
Psychotherapy notes consist of a clinician’s personal observations and interpretations, requiring special handling and separate storage from the general medical record. These notes enjoy unique legal protections, which are only preserved when they are stored independently of the patient’s main chart.
"Storing them in a dedicated, access‑controlled location is not optional. Mixing them into the EHR voids their special protections." – Dr. Danni Steimberg, Licensed Medical Doctor
Psychotherapy notes are distinct from other medical documentation, such as session times, medication monitoring, diagnoses, and progress summaries, which belong in the general medical record.
Rules for Psychotherapy Notes
Psychotherapy notes demand a separate, specific written authorization for disclosure. This authorization cannot be combined with a general medical record release. Even when sharing treatment information with another provider, you must secure explicit written consent for these notes.
There are limited exceptions to this rule. For instance, psychotherapy notes can be used without additional consent for:
- Your own treatment of the patient.
- Supervised training within your practice.
- Defending yourself in legal proceedings initiated by the patient.
- Situations mandated by law, such as reporting abuse or preventing an imminent threat.
Outside these exceptions, explicit authorization is essential. To maintain security, store psychotherapy notes in a restricted section of the EHR with access controls like encryption and multi-factor authentication. For paper records, use locked cabinets in secure areas. When the retention period ends (typically 6–10 years, depending on state law), dispose of the records securely.
Next, consider patient rights and how the minimum necessary rule applies to balance privacy with access.
Patient Rights and the Minimum Necessary Rule
The handling of psychotherapy notes aligns with broader HIPAA regulations, ensuring sensitive data is protected while respecting patient rights.
Under HIPAA, patients generally have the right to access their medical records, but psychotherapy notes are an exception – they are not automatically available to patients. However, patients can access other parts of their records, such as diagnoses, treatment plans, medications, and session summaries. These requests must be fulfilled within 30 days.
If a patient requests changes to their information or places restrictions on how their Protected Health Information (PHI) is shared, document and address these requests promptly. Always verify the patient’s identity before releasing any records. Use standardized authorization forms that clearly outline the specific information to be shared, the recipient’s identity, an expiration date, and the patient’s right to revoke consent.
The minimum necessary rule ensures that only the smallest amount of information needed to fulfill a purpose is disclosed. This applies to routine operational disclosures but does not limit information released directly to the patient or disclosures made with valid authorization. If responding to a broad subpoena for "all records", confirm whether psychotherapy notes are explicitly included. Many such requests can be refined to exclude these sensitive documents.
| Feature | Psychotherapy Notes | Progress/Medical Notes |
|---|---|---|
| Content | Subjective impressions, hypotheses, reflections | Diagnoses, medications, session times, treatment plans |
| Storage | Stored separately from the general record | Integrated within the official medical record |
| Patient Access | Not accessible to the patient under HIPAA | Patients have legal rights to access |
| Authorization | Requires separate, specific authorization | Generally released under standard treatment, payment, and operations consent |
Train Staff and Monitor Compliance
Anyone handling patient information must complete HIPAA training before accessing Protected Health Information (PHI) – this isn’t optional. The Office for Civil Rights (OCR) takes missing or undocumented training seriously, treating it as willful neglect during audits. The consequences can be harsh. For example, in April 2025, PIH Health faced a $600,000 settlement with the OCR after a phishing attack compromised 189,763 patient records. The investigation found that the organization failed to conduct a proper risk analysis and didn’t provide timely breach notifications. Proper training is a critical first step in compliance and safeguarding sensitive patient data.
Training should be tailored to each role. Clinicians need to grasp topics like psychotherapy notes, telehealth consent, and duty-to-warn protocols. Front-desk staff should focus on identity verification, distributing the Notice of Privacy Practices, and securely faxing documents. IT personnel must understand encryption standards, audit log monitoring, and incident response. Billing staff, on the other hand, should be trained in claims security and handling Business Associate Agreements. As James Keogh, Editor at HIPAAnswers, explains:
HIPAA training for mental health professionals should be more thorough than for other health care professionals due to the number of times mental health professionals may be required to make decisions about disclosing Protected Health Information based on their professional judgement.
HIPAA Training Requirements for Staff
New hires must complete HIPAA training within 7 to 30 days of starting their role – and always before they handle patient data. While HIPAA doesn’t specify an annual training requirement, yearly refresher courses are widely considered best practice and are often expected by auditors and insurers. Additionally, retraining is essential whenever there are updates to technology or policies.
To keep HIPAA practices fresh in employees’ minds, supplement formal training with periodic reminders. Use tools like short microlearning modules, phishing simulations, and real-world case studies to reinforce security awareness throughout the year.
Documentation and Internal Audits
Training alone isn’t enough – documentation and audits are just as critical to proving compliance. Keep detailed training records for each employee, including their name, role, training date, topics covered, evidence of understanding (like quiz scores or certificates), and signed acknowledgments. As Complydome emphasizes:
Even if you train your staff, if you can’t prove it, it’s as if it never happened.
A physical therapy clinic in the Midwest learned this the hard way. After a patient complaint triggered an OCR audit, the clinic couldn’t produce documentation to confirm staff training. The OCR found their training was informal and inconsistent, leading to a $35,000 settlement and a corrective action plan that included semi-annual audits and formal training records.
Keep all HIPAA-related documentation for at least six years. A centralized repository with time-stamped approvals and version control can simplify this process.
Internal audits are essential for ensuring policies are followed in daily operations. Conduct annual comprehensive audits that include risk analysis, policy reviews, and system inventories. In addition, perform quarterly mini-audits to check specific areas like remote work security, teletherapy procedures, and mobile device encryption. Regularly review EHR access logs to identify unauthorized access or unusual activity, and periodically spot-check patient charts to ensure disclosures meet the “minimum necessary” standard and access requests are handled promptly.
When audits uncover gaps, categorize findings by severity, assign responsibilities, and set deadlines for corrective actions. Document the resolution process with evidence once issues are addressed. To enforce compliance, implement a tiered sanctions policy – ranging from retraining for minor infractions to termination for serious violations – and apply it consistently across all roles.
Use HIPAA-Compliant Practice Management Tools
Selecting the right software plays a big role in staying HIPAA-compliant. Always choose tools that meet HIPAA’s strict standards and come with a signed Business Associate Agreement (BAA). Without a BAA, you’re legally responsible for any data breaches that happen on their platform.
Good practice management software simplifies complex security requirements, letting you focus more on your clients. Look for features like strong encryption, multi-factor authentication (MFA), and automatic audit logs to track data access and changes. These features are essential for safeguarding sensitive information and meeting compliance needs in mental health practices.
Features of HIPAA-Compliant Software
Mental health practices have specific documentation needs that generic software often doesn’t address. Your software should allow for the separation of psychotherapy notes from the general medical record. This ensures that these highly sensitive notes are stored securely and only disclosed with explicit authorization.
Role-Based Access Control (RBAC) is another must-have feature. It ensures each staff member only sees the information necessary for their role. For practices offering telehealth, look for integrated video conferencing tools with encrypted streams, secure virtual waiting rooms, and disabled recording features to protect client privacy during sessions. If you use voice-to-text dictation, choose vendors that delete audio files immediately after transcription to reduce the risk of data exposure.
How Voice CRM Supports Compliance
Mental health professionals face unique challenges in balancing documentation needs with privacy requirements. Voice CRM is designed specifically for this field, offering secure voice-to-text transcription with end-to-end encryption. It also includes tools for client management, supervision tracking, payment tracking, mood tracking, and thematic tagging – all within a HIPAA-compliant framework.
This all-in-one setup helps maintain the "golden thread" between treatment goals and session progress, a critical aspect for insurance audits and compliance reviews. Voice CRM provides a solution tailored to the specific needs of mental health professionals, making it easier to meet documentation and privacy standards while focusing on client care.
Conclusion
HIPAA compliance isn’t just a box to check – it’s a continuous effort to safeguard both your clients and your practice. As Kevin Henry, a HIPAA Compliance Expert, explains:
By grounding your program in risk analysis, executing BAAs, operationalizing safeguards, and rehearsing incident response, you protect clients and maintain resilient, ethical care.
Building a strong compliance program starts with key steps: appointing a compliance officer, conducting yearly risk assessments, drafting clear policies, and implementing administrative, physical, and technical safeguards. These measures show your dedication to protecting patient information while keeping your practice running smoothly.
Ongoing staff training and regular audits are equally important. They ensure your team stays prepared and your systems remain secure. Don’t forget, HIPAA requires you to retain policies, training records, and risk assessments for at least six years. This documentation is critical for proving compliance during audits and shielding your practice from potential issues.
Using the right tools can make compliance easier. HIPAA-compliant software, like Voice CRM, simplifies processes by automating security requirements. It offers mental health professionals secure voice-to-text transcription, client management, and documentation tools, all within a framework that includes end-to-end encryption and strong safeguards.
Ultimately, protecting patient privacy is about more than just compliance – it’s about trust. In mental health care, trust creates the foundation for a safe and supportive environment. By following these steps consistently, you can ensure your practice is not only legally compliant but also a place where quality care thrives.
FAQs
Do I really need separate Privacy and Security Officers?
Yes, having separate roles for a Privacy Officer and a Security Officer is a good idea to maintain full HIPAA compliance. This is particularly important for mental health practices, which deal with extremely sensitive patient information. That said, the need for separate officers can depend on the size and complexity of your practice.
What qualifies as a major change that requires a new risk assessment?
Major organizational shifts – like mergers, launching new services, deploying major systems, migrating to the cloud, or updating policies and workflows – call for a fresh risk assessment. These kinds of changes can directly affect how sensitive data is handled. Evaluating these shifts is essential to maintaining HIPAA compliance.
How do I keep psychotherapy notes separate in my EHR?
To keep psychotherapy notes separate in your EHR and ensure HIPAA compliance, store them outside the main medical record. This means using safeguards like encryption, role-based access controls, and restricted backups to protect confidentiality.
Psychotherapy notes should focus on subjective reflections, while objective data belongs in progress notes. Make sure your EHR system supports this separation by encrypting psychotherapy notes, granting access only to authorized personnel, and carefully verifying any legal requests before disclosing them.